Once upon a time
in Cyberspace, the three little pigs were settling down for the night. It had been a long time since
they had any problems from the wolf, and they were starting to forget about the danger he once posed to
them. As long as
they were in the house made of brick, they felt safe from any danger. The house was equipped with state
of the art
monitoring and surveillance. The pigs could lock and unlock the doors remotely, see who was at the door
without even
leaving the couch with their video doorbell, and see every inch of the perimeter with cameras all over
the house.
They felt extremely comfortable with their defenses.
Once upon a time
in Cyberspace, the three little pigs were settling down for the night. It had been a long time since
they had any problems from the wolf, and they were starting to forget about the danger he once posed to
them. As long as
they were in the house made of brick, they felt safe from any danger. The house was equipped with state
of the art
monitoring and surveillance. The pigs could lock and unlock the doors remotely, see who was at the door
without even
leaving the couch with their video doorbell, and see every inch of the perimeter with cameras all over
the house.
They felt extremely comfortable with their defenses. 
The wolf, however, was still brooding over his earlier defeat and vowed to get even. He knew he could not
defeat the
physical defenses of the brick house, so he devised a new plan to gain access to the pigs. He decided to
do some OSINT research on the them. (Open-Source Intelligence) research refers to the process of
collecting and analyzing publicly available information
from various sources, such as the internet, social media, and public records, to gather intelligence and
insights about
individuals, organizations, or events. He conducted external scans of their network, he dug through
their trash, googled them, and stalked their social media profiles. It was here he found out that Piggie3 liked to post pictures of cats on her InstaTikFace social media profile.
 The wolf, being a
cunning and tech-savvy predator, recognized the power of information in the digital age. Armed with
this newfound knowledge about Piggie3's interests, he hatched a plan to exploit it. He knew that
the pigs'
sense of security was rooted in their advanced technology and that they might let their guard down if
they believed
there was no immediate threat. So he stayed out of sight while he enacted his plan. "Those pigs would never see this coming!", he thought.
The wolf, being a
cunning and tech-savvy predator, recognized the power of information in the digital age. Armed with
this newfound knowledge about Piggie3's interests, he hatched a plan to exploit it. He knew that
the pigs'
sense of security was rooted in their advanced technology and that they might let their guard down if
they believed
there was no immediate threat. So he stayed out of sight while he enacted his plan. "Those pigs would never see this coming!", he thought.
The wolf created a fake social media account, posing as a fellow cat enthusiast. He began engaging with
the pig's cat
posts, liking and commenting on them, gradually building a virtual friendship. Piggie3, not suspecting
any danger,
happily accepted the wolf's friend request and engaged in conversations about their shared love for
cats. Over time,
the wolf carefully steered the conversations towards personal details, subtly gathering information
about the pig's
routines and habits. He learned about the pig's favorite time to check his social media, her daily
schedule, and
even her upcoming plans. One day, as the wolf was chatting with the pig, he noticed a post mentioning
that she
was planning to have a big party at the brick house the following evening. The wolf couldn't believe
his luck. He
had just stumbled upon the perfect opportunity to strike. With this newfound information, the wolf
decided to use
social engineering to bypass the pigs' high-tech security measures. Using his fake InstaTikFace profile @hereKitty1, he reached out to the Piggie3 and asked if he could
bring a very special and rare breed of cat to the party, claiming it would be a surprise gift for the host. Piggie3 unsuspecting of her new friend and flattered by the offer, gladly accepted.
 The next evening, as the Piggie3 and her guests were enjoying the party inside the seemingly impenetrable
brick house,
the wolf would arrive carrying a very "special" cat. As soon as the door was opened to let him in, the wolf
would spring into
action. He would conceal a small hacking device capable of disabling the house's security systems
temporarily. While the partygoers were distracted by the "special" cat, the wolf would activate the
device, causing a
brief blackout in the house's surveillance and security systems.
The next evening, as the Piggie3 and her guests were enjoying the party inside the seemingly impenetrable
brick house,
the wolf would arrive carrying a very "special" cat. As soon as the door was opened to let him in, the wolf
would spring into
action. He would conceal a small hacking device capable of disabling the house's security systems
temporarily. While the partygoers were distracted by the "special" cat, the wolf would activate the
device, causing a
brief blackout in the house's surveillance and security systems. 
The wolf's cunning plan paid off. As he arrived at the pigs' party with the "special" cat, the door
opened to
welcome him inside. The pigs, trusting their advanced security systems, momentarily had let their guard
down. With the
flick of a switch on his hacking device, the wolf exploited a vulnerability in the house's security
software,
disabling all surveillance and locking mechanisms. Seizing the opportunity, he lunged forward and made
a desperate attempt to breach the brick walls. The pigs, startled by the blackout, were unable to react
quickly
enough and failed to reinforced their defenses.
 Once inside, the
wolf didn't harm the pigs but instead gave them a stern lecture on the importance of cybersecurity.
He reminded them of their successes in their previous engagement before their tech impementation and on
how they were not as sharp as they used to be. He had a much harder time gaining access to the facility
before they started relying soley on technology to keep them safe. The pigs listened intently, realizing
the gravity of their mistake.
Once inside, the
wolf didn't harm the pigs but instead gave them a stern lecture on the importance of cybersecurity.
He reminded them of their successes in their previous engagement before their tech impementation and on
how they were not as sharp as they used to be. He had a much harder time gaining access to the facility
before they started relying soley on technology to keep them safe. The pigs listened intently, realizing
the gravity of their mistake.
 The wolf went on
to provide a detailed report of the vulnerabilities he had discovered during the exercise. He
explained how their overreliance on technology and their tendency to share personal information online
had made them
vulnerable. The pigs were grateful for the wake-up call and the opportunity to strengthen their security
measures.
With the guidance of the wolf's vulnerability report, the pigs began to patch their vulnerabilities,
fortify their digital and physical defenses, as well as implement best practices for cybersecurity. They
knew that ongoing security assessments and proactive measures
were crucial to staying safe in the modern age of Cyberspace.
The wolf went on
to provide a detailed report of the vulnerabilities he had discovered during the exercise. He
explained how their overreliance on technology and their tendency to share personal information online
had made them
vulnerable. The pigs were grateful for the wake-up call and the opportunity to strengthen their security
measures.
With the guidance of the wolf's vulnerability report, the pigs began to patch their vulnerabilities,
fortify their digital and physical defenses, as well as implement best practices for cybersecurity. They
knew that ongoing security assessments and proactive measures
were crucial to staying safe in the modern age of Cyberspace.
After the post-mortem was concluded the pigs made the check out to LoneWolf PenTesters and the wolf took
his leave. The pigs worked on remediating the remaining issues found during their pentest engagement.
The score was now 1 to 1. They'd be ready for the wolf the next time.
In the end, the pigs and
the wolf shared a sense of accomplishment, knowing that the successful penetration test had
ultimately strengthened their security posture.






 About
Me
DJames617.com
HDJames.com
Nerddual.com
About
Me
DJames617.com
HDJames.com
Nerddual.com
 Happy New Year Everyone!!
Happy New Year Everyone!! The Wolf Gets Even
The Wolf Gets Even
 Once upon a time
in Cyberspace, the three little pigs were settling down for the night. It had been a long time since
they had any problems from the wolf, and they were starting to forget about the danger he once posed to
them. As long as
they were in the house made of brick, they felt safe from any danger. The house was equipped with state
of the art
monitoring and surveillance. The pigs could lock and unlock the doors remotely, see who was at the door
without even
leaving the couch with their video doorbell, and see every inch of the perimeter with cameras all over
the house.
They felt extremely comfortable with their defenses.
Once upon a time
in Cyberspace, the three little pigs were settling down for the night. It had been a long time since
they had any problems from the wolf, and they were starting to forget about the danger he once posed to
them. As long as
they were in the house made of brick, they felt safe from any danger. The house was equipped with state
of the art
monitoring and surveillance. The pigs could lock and unlock the doors remotely, see who was at the door
without even
leaving the couch with their video doorbell, and see every inch of the perimeter with cameras all over
the house.
They felt extremely comfortable with their defenses. 
 The wolf, being a
cunning and tech-savvy predator, recognized the power of information in the digital age. Armed with
this newfound knowledge about Piggie3's interests, he hatched a plan to exploit it. He knew that
the pigs'
sense of security was rooted in their advanced technology and that they might let their guard down if
they believed
there was no immediate threat. So he stayed out of sight while he enacted his plan. "Those pigs would never see this coming!", he thought.
The wolf, being a
cunning and tech-savvy predator, recognized the power of information in the digital age. Armed with
this newfound knowledge about Piggie3's interests, he hatched a plan to exploit it. He knew that
the pigs'
sense of security was rooted in their advanced technology and that they might let their guard down if
they believed
there was no immediate threat. So he stayed out of sight while he enacted his plan. "Those pigs would never see this coming!", he thought.
 The next evening, as the Piggie3 and her guests were enjoying the party inside the seemingly impenetrable
brick house,
the wolf would arrive carrying a very "special" cat. As soon as the door was opened to let him in, the wolf
would spring into
action. He would conceal a small hacking device capable of disabling the house's security systems
temporarily. While the partygoers were distracted by the "special" cat, the wolf would activate the
device, causing a
brief blackout in the house's surveillance and security systems.
The next evening, as the Piggie3 and her guests were enjoying the party inside the seemingly impenetrable
brick house,
the wolf would arrive carrying a very "special" cat. As soon as the door was opened to let him in, the wolf
would spring into
action. He would conceal a small hacking device capable of disabling the house's security systems
temporarily. While the partygoers were distracted by the "special" cat, the wolf would activate the
device, causing a
brief blackout in the house's surveillance and security systems. 
 Once inside, the
wolf didn't harm the pigs but instead gave them a stern lecture on the importance of cybersecurity.
He reminded them of their successes in their previous engagement before their tech impementation and on
how they were not as sharp as they used to be. He had a much harder time gaining access to the facility
before they started relying soley on technology to keep them safe. The pigs listened intently, realizing
the gravity of their mistake.
Once inside, the
wolf didn't harm the pigs but instead gave them a stern lecture on the importance of cybersecurity.
He reminded them of their successes in their previous engagement before their tech impementation and on
how they were not as sharp as they used to be. He had a much harder time gaining access to the facility
before they started relying soley on technology to keep them safe. The pigs listened intently, realizing
the gravity of their mistake.  The wolf went on
to provide a detailed report of the vulnerabilities he had discovered during the exercise. He
explained how their overreliance on technology and their tendency to share personal information online
had made them
vulnerable. The pigs were grateful for the wake-up call and the opportunity to strengthen their security
measures.
With the guidance of the wolf's vulnerability report, the pigs began to patch their vulnerabilities,
fortify their digital and physical defenses, as well as implement best practices for cybersecurity. They
knew that ongoing security assessments and proactive measures
were crucial to staying safe in the modern age of Cyberspace.
The wolf went on
to provide a detailed report of the vulnerabilities he had discovered during the exercise. He
explained how their overreliance on technology and their tendency to share personal information online
had made them
vulnerable. The pigs were grateful for the wake-up call and the opportunity to strengthen their security
measures.
With the guidance of the wolf's vulnerability report, the pigs began to patch their vulnerabilities,
fortify their digital and physical defenses, as well as implement best practices for cybersecurity. They
knew that ongoing security assessments and proactive measures
were crucial to staying safe in the modern age of Cyberspace. 
 2024 Updates
2024 Updates 
 I am DJames617, AKA Ne'er-Do-Well nerd. Welcome to
I am DJames617, AKA Ne'er-Do-Well nerd. Welcome to 
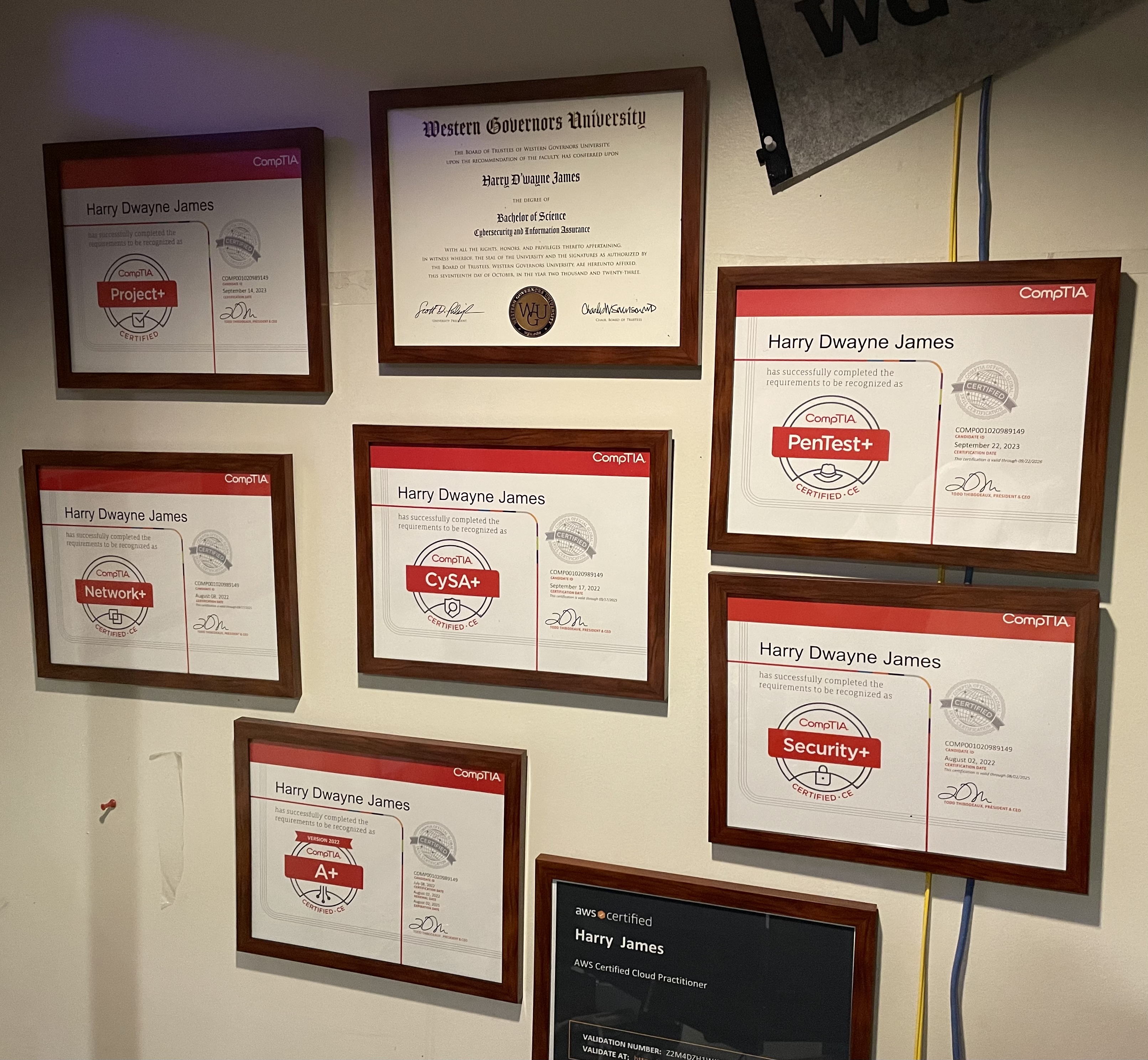
 My first set of COMPTia certs (A+, Network+, and Security+)
are lifetime
and don't expire. They also did not count for credit at WGU. When I had to take another A+
course I was a
bit annoyed. Then I realized that passing this class would get me closer to the degree. It got much
easier after
that realization. I now have 2 sets of CompTia certs, but I only have to renew one. WGU is a great
school for
people who have expierience and need a degree. You set the schedule. Take classes when you have the
time, live
your life the rest of it.
My first set of COMPTia certs (A+, Network+, and Security+)
are lifetime
and don't expire. They also did not count for credit at WGU. When I had to take another A+
course I was a
bit annoyed. Then I realized that passing this class would get me closer to the degree. It got much
easier after
that realization. I now have 2 sets of CompTia certs, but I only have to renew one. WGU is a great
school for
people who have expierience and need a degree. You set the schedule. Take classes when you have the
time, live
your life the rest of it.  If you need hand holding in order to learn, WGU is probably
not going to work well for you. I found they don't really teach as much as they evaluate.
It is based on the compentency model where you show what you know. You only spend time learning
things you
can't test out of. Why spend time in a class that you can pass right away?
If you need hand holding in order to learn, WGU is probably
not going to work well for you. I found they don't really teach as much as they evaluate.
It is based on the compentency model where you show what you know. You only spend time learning
things you
can't test out of. Why spend time in a class that you can pass right away?